In the coming years, this technology will fundamentally change the issue of personal privacy breaches
The author of this article is Packy McCormick, translated by Dama Hiyu.
Recently, the serious illegal use of personal information by the "Didi Chuxing" app has captured public attention, leading more people to become concerned and worried about personal data privacy. Many times, individuals and organizations share privacy and accept their insecurity, seemingly as a necessary sacrifice for the smooth operation of modern society. But will it always be this way?
Last month, Packy McCormick wrote an article about "zero-knowledge proofs," discussing how to address the issue of personal privacy security. If you are interested in new technologies and personal privacy, this will be a great piece of popular science on new technology.
Here is the translated content based on the original text, with some parts omitted. Enjoy :)
Every so often, a technology emerges that appropriately combines promise, ambiguity, elusiveness, and abstraction, capturing and igniting the imagination of collective thought. These technologies not only change a few things; they are likely to change everything.
For example, blockchain, artificial intelligence, chatbots, cloud computing, VR, autonomy, Metaverse, mRNA, etc.
Initially, new technologies are like a blank canvas, where people can freely express their hopes and ideas, while some vendors package them as "panaceas" to deceive the public.
When someone first proposes how to use this technology to accomplish tasks, and before practitioners begin the arduous work of these technologies, its possibilities are vast. As high school physics teaches us, the kinetic energy is at its highest before it is consumed. The same applies here.
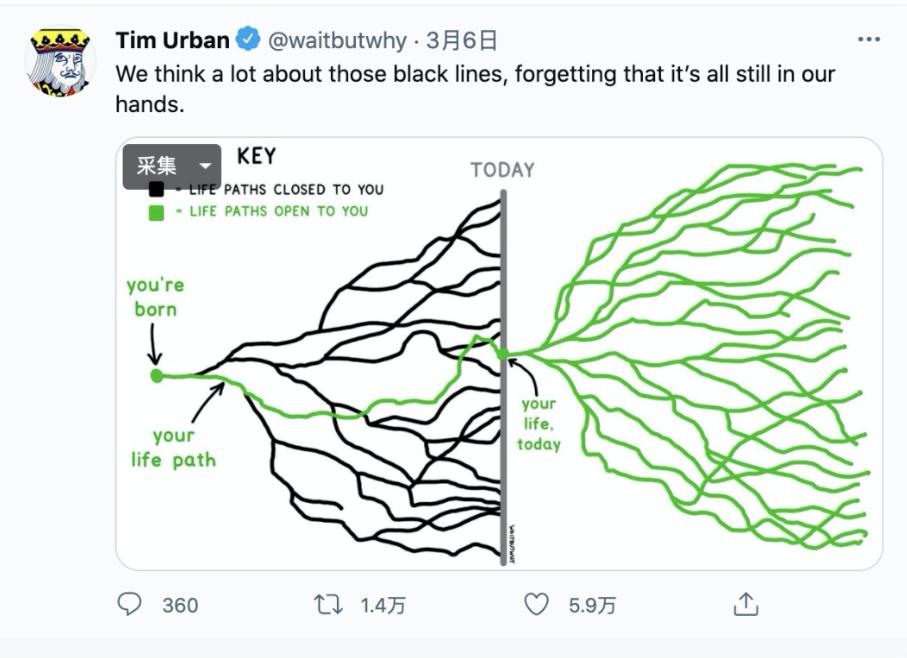
A picture from Tim Urban's "Wait But Why" illustrates this point well. When nothing has been done, all possibilities are open and unknown.
By the way, this is also why raising venture capital with just an idea, a platform, or even a prototype is easier than when your product is in the hands of customers and has already generated some revenue. It may also explain why the audience for the NBA draft is twice that of regular national television broadcasts. Because people love potential.
This dynamic helps explain the chart we are about to show you: the Gartner Hype Cycle (also known as the technology maturity curve).
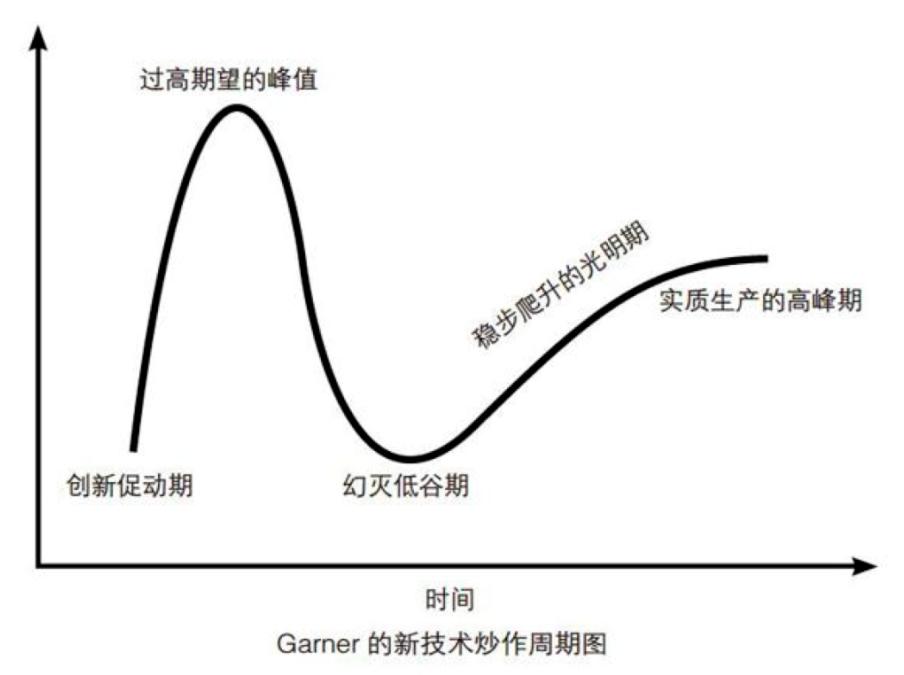
Gartner's "Hype Cycle" is incredibly consistent. Every promising new innovation goes through this cycle, which seems to be a kind of "ritual." The effectiveness of the hype cycle lies in its reflection of our predictable group behavior, mocking us a bit: "You will be very excited about this thing, and it will all collapse, just watch. But don't worry, it sometimes rebounds."
Part of the fun is identifying those things that have just experienced technological germination and intervening super early, building, investing, and thinking about them before others have even heard of these technologies. But my technical skills are far from sufficient to figure out when these technological triggers occur.
I keep track of smart people on Twitter and engage in discussions and research with friends.
A few weeks ago, my friend Jill Carlson (Jill Carlson) made another prediction about what zero-knowledge proofs are.
Jill graduated from Harvard University, is a co-founder of the Open Money Initiative, and is an investor. She is much smarter than I am, so when she makes predictions, I listen. Fortunately, Mr. Fox took notes for me, and Jill and I decided to team up to explain what zero-knowledge proofs (ZKPs) are, why they are important, and their potential applications.
Zero-knowledge proofs essentially allow me to prove to someone that I know or possess something without revealing the specific information I know.
For example, I can prove that I know the password to an account without risking exposure by entering the password. Or I can prove that I have enough money to pay next year's rent without disclosing the details of my personal finances or my bank statements.
This technology impacts personal privacy, cryptocurrency, business, and even nuclear disarmament. What is exciting about zero-knowledge proofs is that they have the potential to eliminate the inherent trade-offs in life, work, and online transactions: the internet exchanges our privacy for its convenience, speed, reach, and scale.
Today, we will take a glimpse into this future and its implications, and I will elaborate on six aspects.
• What are zero-knowledge proofs?
• The history of zero-knowledge
• The benefits of hype
• The scope of privacy
• Applications of zero-knowledge systems
• The design space of zero-knowledge
Let's start with what zero-knowledge proofs are.
What are zero-knowledge proofs?
Our data is everywhere. Names, birth dates, email addresses, credit card numbers, past five years of addresses, and even mother's maiden names… and these are just a few of the nearly infinite pieces of information we provide to companies, social media sites, and sometimes (unwittingly) to scammers every day.
The problems arising from this situation are self-evident. Identity theft, email breaches, data leaks, and other forms of fraud cost individuals and businesses hundreds of billions of dollars each year, and the spending on defense and prevention is several times more than that, not to mention how painful it is to deal with the consequences.
As participants in the modern interconnected world, the explosion of data and its associated vulnerabilities have become an acknowledged cost of doing business, and we must trust each other. We have to enter our credit card numbers on websites. Send our credit records to landlords, provide our identification documents to banks.
Not only individuals but also companies and organizations must continuously disclose sensitive information to one another to operate their businesses. Sharing privacy and accepting insecurity seems to be a necessary sacrifice we make for the smooth operation of modern society.
But what if there were a way to interact and transact with the same level of trust and certainty without sharing all this data? Well, thanks to some tricky mathematics, which even cryptographers consider "moon math," they discovered zero-knowledge proofs.
With this technology, I can prove to you that I know certain things without revealing the specific information I know. I know you might still be a bit confused, so let me give you an example without involving "moon math."
Case One
My colorblind friend and I are looking at balls on the table, where one is red, one is green, and the rest are the same. When I tell him there are two different colors, he is unsure whether to believe me. We decide to play a game to determine if they are indeed different colors.
• I give him two balls to hide behind his back,
• He takes one ball out to show me,
• Then he puts that ball back behind his back, retrieves another ball, and asks, "Did I switch balls?"
If we repeat this game enough times, if I correctly answer whether he switched balls each time (even though he is colorblind, he knows whether he switched balls), then I will have proven to him that these balls are definitely two different colors. Importantly, I have proven to him that the balls are of two colors without revealing any other information. Perhaps frustratingly for him, he still does not know which ball is red and which is green.
There are many such explanations out there. If you want to see an earlier, even child-friendly explanation, you can check this link: http://pages.cs.wisc.edu/~mkowalcz/628.pdf.
The original paper on zero-knowledge proofs states: "It conveys no other knowledge beyond the correctness of the proposition being discussed."
The History of Zero-Knowledge
Zero-knowledge proofs are not new: they were first proposed by researchers Shafi Goldwasser, Silvio Micali, and Charles Rackoff at MIT in the 1980s.
These three were studying a concept called interactive proof systems. In such systems, there are two parties: one is a prover of certain information, and the other is a verifier of that information. Generally, in these systems, it is assumed that the prover cannot be trusted, while the verifier can be trusted. The goal of the system is to be designed in such a way that:
The verifier can trust the truthful statements of the untrusted prover,
The prover cannot convince the verifier to believe an untrue statement.
Think of it this way: I am outside a bar, and a bouncer is standing at the door, asking to check my ID. In this case, I am the prover (I need to prove I am of legal age), and the bouncer is the verifier. If the bouncer and I use an interactive proof system and see my ID showing that I am over 21, then I can prove to him that I am of legal age. If someone behind me is underage (the prover), he will not be able to convince the bouncer to let him in. That is, the prover cannot convince the verifier to believe an untrue statement.
Then, Goldwasser, Micali, and Rackoff added an extra layer of complexity to the interaction. They posed (and answered) the question: What if neither the bouncer can be trusted nor I can trust the bouncer? Perhaps I suspect the bouncer is stealing people's identities, or maybe I don't want him to know that I am a Taurus. Whatever the issue, suddenly, the prover does not want the verifier to know their underlying information.
More specifically, Goldwasser, Micali, and Rackoff were concerned about the issue of information leakage. They posed the thought: "How much additional information, purely about the truth of the verification statement, is obtained during the verifier's verification process without needing to know?"
In the 1980s and 1990s, zero-knowledge proofs were further studied in academia, but there was little practical implementation or use. It wasn't until the 21st century that researchers and entrepreneurs began applying the theory to real-world applications.
In the mid-2000s, one of the earliest applications of zero-knowledge proofs was in password security.
When you log into a website using a password, what typically happens is that you enter your password and send it to the server, which hashes your password into a string of gibberish and compares it to see if it matches the gibberish stored next to your name in their system.
If the values match, you get in. The gibberish is a layer of password protection that prevents companies or anyone from storing your password in plain text. However, there is still a problem: you are still disclosing your password to the server in the first place. That year, a protocol was discovered that used zero-knowledge proofs to address this vulnerability, spanning 139 pages. This was one of the earliest examples of zero-knowledge proofs applied to real-world problems.
In 2013 and 2014, zero-knowledge proofs found commercial applications in another system that had been incubating in academia for many years before being introduced to the world: cryptocurrency. Despite its reputation for illegal transactions, one core feature of Bitcoin and most other cryptocurrencies is that everything that happens is publicly recorded.
This led to Zcash (initially called Zerocash, and its predecessor Zerocoin). Launched in 2016, Zcash is a cryptocurrency created using a specific type of zero-knowledge system, maintaining the decentralized properties of Bitcoin while introducing privacy features closer to physical cash—meaning almost complete untraceability.
In Zcash, zero-knowledge proofs specifically enable the network of computers running the Zcash protocol to verify that each transaction is valid (i.e., I indeed have the 10 Zcash I am sending you) while keeping the transaction data private.
If you want to learn more, you can listen to this episode of Radiolab about Zcash from 2017: https://open.spotify.com/episode/4w8w75pHSnKuoRsNqm9Tvt
Zcash and other privacy-oriented cryptocurrencies have attracted significant attention and funding. All this money and attention have propelled groundbreaking advancements in zero-knowledge systems.
A new generation of efficient zero-knowledge proofs has been developed, addressing many of the cumbersome, tedious, expensive, and controversial issues surrounding these systems. (If you have listened to that RadioLab episode, you will find that many of the issues discussed then are no longer problems.)
Optimizations have accelerated the tremendous progress of these systems, and a new and larger community of builders has emerged, with active open-source development libraries accelerating development and improving performance.
The moment for zero-knowledge systems to take off has finally arrived.
The Benefits of "Hype"
Let's take a moment to look at the positive impact of marketing and commercialization, namely the benefits of "hype."
Zero-knowledge proofs have existed in academia for decades, predating Tim Berners-Lee's invention of the World Wide Web. If our internet predecessors had embedded zero-knowledge systems into the web, the world might be very different. As long as people want to reap the benefits of the internet without trading their privacy, research into zero-knowledge proofs is important work.
But zero-knowledge proofs remained a niche interest of quirky mathematicians and cryptographers until a way was found to combine technology and business.
Zcash sparked a new wave of interest in zero-knowledge proof research and increased interest from investors and entrepreneurs. In the next five years, there will be more work on zero-knowledge proofs and their applications than in the previous thirty-six years combined.
This is actually a common phenomenon. Hype and speculation attract resources that help solve difficult problems, satisfying the demands of hype while rewarding some speculators. Rather than dismissing hype and speculation, it is better to understand their purpose. They make innovation possible.
Let’s take two examples: Bitcoin and mRNA.
Satoshi Nakamoto's true innovation with Bitcoin was solving the double-spending problem. Double spending: In a digital currency system, due to the replicability of data, the system may face the situation where the same digital asset is improperly reused. This is a well-known problem that researchers have not found a solution to for decades, hindering the adoption and development of digital currency.
Bitcoin, whether through technological innovation or the speculation it sparked, released enormous financial and human capital and triggered a financial renaissance.
Outside of cryptography, mRNA also provides a relevant example of the same phenomenon. As early as the 1970s, Dr. Katalin Karikó saw the potential of mRNA, which transmits information from DNA to ribosomes to determine which proteins to manufacture.
For nearly 50 years, she struggled to get anyone to take its potential seriously. Then, in 2020, Karikó's work contributed to the development of Pfizer's mRNA-based COVID-19 vaccine, which will save millions of lives and generate billions in profits.
Now, mRNA is being hailed as a potential cure for all our diseases. "The impact of mRNA technology is astounding," Swati Gupta of Yale University wrote in May, "Some vaccine developers are exploring this technology to tackle rabies, influenza, Zika virus, HIV, and cancer, as well as veterinary applications. The commercial success of mRNA and the global devastation of COVID-19 have opened up a whole new design space for biotechnology.
Today's zero-knowledge proofs are in the same position as mRNA a few years ago and the double-spending problem a decade ago. Privacy has more commercial possibilities.
The Scope of Privacy
When it comes to privacy issues, there are two camps.
Those who have already given up. They believe that all their data can be provided to those who really need privacy. Here, "really" refers to some legitimate institutions and companies, but even these legitimate companies, can they guarantee that they won't leak our privacy?
Those who truly care about privacy.
Most of us belong to the first camp. Of course, we update our passwords from time to time, and we imagine that hackers won't steal our data, but when we have so much information living online, maintaining true privacy is more work than we are willing to undertake.
In other words, most of us are willing to trade privacy for convenience.
Zero-knowledge proofs have the potential to eliminate the trade-off between privacy and convenience and bring about a paradigm shift in how we think about privacy. We can ask: "Who really needs how much information, and under what circumstances, rather than a black-and-white decision to take all my information at once?"
Through zero-knowledge proofs, people can know only the information they need to know without needing to know what they do not need to know. They do not need to acquire all your data to still verify what they need to verify.
Companies like Stytch and Magic are providing developers with a toolkit for passwordless authentication in a more secure and faster way.
Evervault builds encryption infrastructure for developers, ensuring that any data entered by users is automatically encrypted at the field level, never existing in unencrypted form in the company's database, and can only be processed in a "privacy cage."
Evervault is helping businesses that need to handle highly sensitive data (such as location data, bank account data, payment data, children's data, corporate data, and health data) to develop APIs together.
In its eight-point pragmatic privacy declaration, Evervault perfectly captures the spirit of the new generation of privacy technologies: privacy is a fundamental expectation and human right, but it should never slow down the pace of technological advancement.
In other words, we no longer need to accept historical concessions on privacy.
The purpose of zero-knowledge proofs is also to eliminate the trade-off between privacy and convenience, but the approach is different. They ask, "What if this data was never exchanged in the first place?" The answer has broad implications and applications.
Applications of Zero-Knowledge Systems
It is difficult to truly understand the significance of zero-knowledge proofs without some practical applications. Let's start with a simple example to illustrate why zero-knowledge proofs are valuable and how they work, then move on to some more complex examples.
A Personal Example of Renting an Apartment
After a wonderful gap year in New Jersey, Pujia and I are preparing to move back to Brooklyn. One day, we visited an apartment where we first met our broker, Dolores. After about 10 minutes, we liked the apartment, so we told Dolores that we wanted to submit an application to rent it.
"Great!" she said, "Just fill out the PDF, and email me your bank statements and proof of income, along with both of your social security numbers, and we can do a credit check."
With all due respect, we just met, and there's no reason for me to believe she won't violate my privacy. I don't want her and her team to see the ins and outs of our financial lives, and I don't quite trust her to ensure that hackers can't access this data.
Using a zero-knowledge system, we can prove to Dolores that we have good credit and 40 times the monthly rent without having to share our social security numbers or any actual data that supports that assumption.
Clear? Not clear. Well, let me explain what happens in that zero-knowledge proof box.
This is still a relatively simple example, but it is more complex than the previous red-green ball problem because in this case, we need to prove not just that two things are different, but that a number is greater than the required number. This applies to both credit scores and income.
We can illustrate how zero-knowledge proofs work at a more advanced level using the income example.
Let's say the rent for the apartment is $1,000 per month, and to qualify for the lease, we need to earn at least 40 times the rent, meaning we need to prove that we earn at least $40,000 a year. Dolores doesn't want us to game the system, so she doesn't tell us what the rent is.
Here’s how she tests us.
There are ten boxes, labeled in increments of $10,000, from $10,000 to $100,000. Each box has a key and a paper-width slot. Dolores first enters the room with the boxes, destroys nine keys, and then takes the key for the box labeled $40,000.
Then Pujia and I enter the room with ten slips of paper. We mark each slip with a "+" or "-" depending on whether the income in each box is below or above our income. For example, if we earn $75,000, we put "+" slips in the first seven boxes and "-" slips in the last three boxes.
We leave the room, and Dolores goes back in. She uses the key to open the $40,000 box. Inside, she finds a "+". She knows that our income exceeds the $40,000 requirement, and we qualify to rent the apartment, and she never discovered what our actual income is.
Of course, for the example above, zero-knowledge proofs might be a bit overkill; using Truework (an identity verification platform in the U.S.) might be a better solution, but who knows, maybe one day zero-knowledge proofs will be used. This is what happens at the beginning of the hype cycle: people try to apply new technologies everywhere, even if it is overkill.
More Complex Examples
In the alternative realm of cryptocurrency, the kind of interaction described in the "renting an apartment" example has become possible. Today, there are projects working to use zero-knowledge proofs to prove traders' credit scores, and others focusing on bringing zero-knowledge proof-based privacy to Ethereum.
All these innovations have the potential to open up cryptocurrency and its applications to users who have thus far been excluded.
Today, you don't see many businesses using stablecoins to issue international payrolls, even though they have proven to be more effective than wire transfers. One key reason is that such companies cannot casually leak their financial information and transaction history on the internet; they worry about data privacy issues. And the vast majority of blockchains do not even meet the minimum standards for data privacy protection.
So why don't these businesses use something like Zcash? Because in addition to concerns about data security, these businesses must also worry about compliance. They cannot use something that is completely on the other end of the privacy spectrum because they lack an audit trail to prove they are paying known transaction parties and not funding terrorist organizations. Yes, these are real issues companies must worry about, not just movie plotlines like "Burn's Identity."
One cool aspect of the zero-knowledge proofs being developed today is that they not only facilitate privacy features but also promote selective disclosure of knowledge. So now you can imagine (and build) a stablecoin product that meets both the data needs of companies and compliance requirements: the issuer of such an asset can have a complete audit trail and be able to verify the compliance status of all holders, while to the majority of the world, this asset flows privately in anonymous accounts.
Zero-knowledge proofs are also being utilized to scale Ethereum. A scheme called zk-Rollups promises to reduce the fees users pay on Ethereum transactions and improve the throughput and scalability of the Ethereum blockchain. zk-Rollups reduce the computational and storage resources used to validate blocks by decreasing the amount of data stored in transactions. More cool work being done in this area can be found here: https://medium.com/matter-labs/introducing-matter-testnet-502fab5a6f17.
You might ask, as a non-cryptographer, why should I care about this?
While most of the innovations surrounding zero-knowledge proofs have been pioneered in the cryptocurrency space, their impact and applications are much broader.
For example, cloud infrastructure can become more secure using these zero-knowledge proofs (without needing cryptocurrency). Users can leverage cloud computing without exposing sensitive consumer data to cloud providers. This is particularly important for industries like financial services, government, and other risk-averse entities. These industries have lagged in adopting hosted cloud infrastructure, which has left visionary CTOs, cost-sensitive CFOs, and users craving a more modern experience feeling very frustrated.
If zero-knowledge proofs can enable these industries to start using cloud computing providers without trusting those who hold sensitive data, then a revolution is waiting to happen.
These are just some applications of zero-knowledge systems waiting for us to explore in the coming years. Remember: we are still just at the technological trigger point of the "hype cycle," and we are unlikely to have a concrete understanding of the performance of the zero-knowledge revolution until we experience the peaks and troughs and find ourselves on the slope of enlightenment years later.
The Outlook for Zero-Knowledge
Grabbing onto something early in the "hype cycle" is most exciting for the new design space and experimental opportunities that the technological trigger point brings. This is an imaginative time where anything that can happen may happen.
From the trigger of technology to the peak of inflated expectations, it is all about seeing which ideas will succeed, which will not, and which things even early space explorers did not think of.
When the market masters new infrastructure, millions of people's wild dreams and ideas clash with technological and societal constraints, and then, due to limiting factors, they taste temporary victories, excitement in this space suddenly declines, but builders keep building, persisting in applying new technologies to real use cases.
Today, we are still at the trigger point of technology, at the foot of the mountain, so we can dream a little.
Zero-knowledge proofs are incredible, hopeful, and exciting, but don't be surprised if expectations exceed reality in the short term. There are daunting technical, economic, and social challenges to solve, and let’s be realistic, nothing fuels "hype" more than zero-knowledge.































