TokenPocket exchange service provider was hacked, please check how many "unlimited authorizations" you have enabled
Author: Loopy Lu, Planet Daily Odaily
Today, the cross-chain DEX aggregator Transit Swap was attacked, resulting in a large amount of user funds being withdrawn from wallets. As of now, the estimated loss exceeds $21 million.
After discovering the theft, the Transit Swap technical team urgently suspended services, and the contract has been completely paused, preventing any operations. Before publication, Transit Swap's official announcement stated that the reason for the previous hacker attack was a code error. The hacker's IP address, email address, and related on-chain addresses have been identified. The Transit Swap team stated that they will do their best to track the hacker and attempt to communicate with them to help users recover their losses.
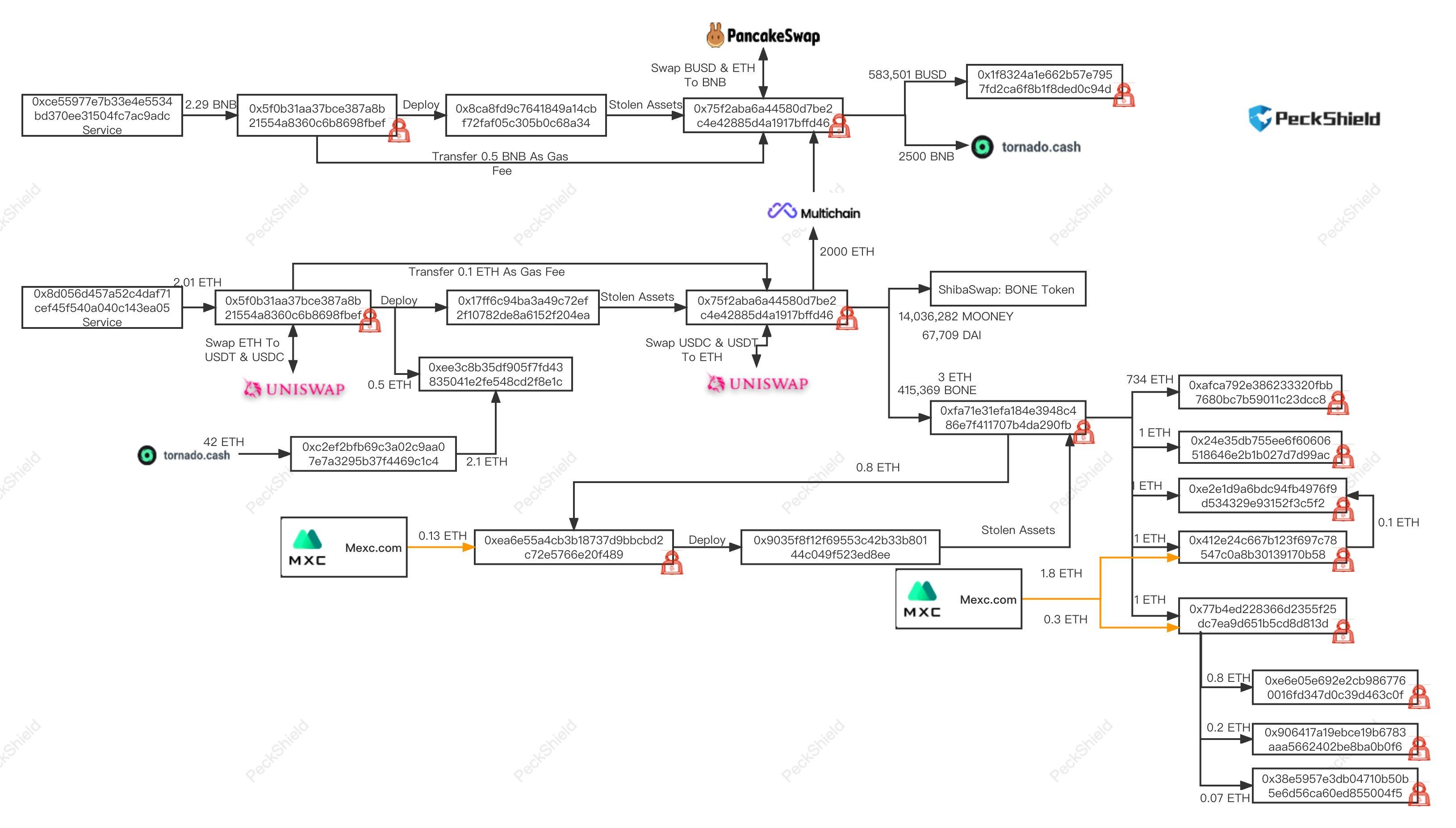
In addition, the security team PeckShield has confirmed the flow of the hacker's funds.
Unlike previous theft incidents, Transit Swap is a flash exchange service provider for the TokenPocket wallet. This allowed a large number of users to experience a "seamless theft" experience, further clarifying the terrifying rule of the "dark forest" in the crypto market: even the convenient "flash exchange" service backed by wallets still carries the risk of theft.
What is Flash Exchange?
Currently, almost all wallets have integrated DeFi functions, and some wallets have created and applied the concept of "flash exchange" for ease of use.
A flash exchange is deeply integrated with the wallet, featuring a more obvious independent entry point, a simplified operation process, and more convenient operations. Users can easily and quickly complete cryptocurrency asset transactions using flash exchanges. For example, the "Approve" operation is often simply integrated into the transaction process with one click, making it almost imperceptible for users.
Due to the built-in integration within the wallet, users naturally have more trust in it, which also reduces their awareness of prevention to some extent. However, at its core, it is just a DEX integrated into the wallet app, which is no different from other DEXs. This also leaves hidden dangers for this security incident.
How Much Risk is Hidden in Contract Authorization?
"No one can forcibly take your crypto assets," is a widespread consensus among investors regarding the characteristics of blockchain. Once on-chain assets are owned by a wallet, there are no coercive means to transfer them. But when we use a DEX for on-chain transactions, how does the DEX take one asset and transfer another to you?
Authorization becomes the key to all of this. Before users sell assets on a DEX, they must first perform the "Approve" operation, after which the contract gains the authority to utilize a certain token of the user.
To put it more plainly: as long as you have authorized, without needing to open the wallet, perform operations, or use a private key, the contract can manage the assets you have authorized without your permission. This is determined by Ethereum's mechanism and authorization model, and has no relation to the project's ethical standards, security norms, or code audits.
Audit = Security?
Even if the contract has the ability to transfer crypto assets after authorization, this ability is still safe as long as it is used within a reasonable scope. But does an audit by a trusted security agency mean that this ability will not be abused and will only transfer the necessary assets for the user’s transactions?
From a static perspective, this logic holds. Just like Uniswap has the ability to empty a user's wallet at any time, but does not actually do so. However, from a dynamic perspective, this logic remains dangerous.
Modern software development requires upgrades as an essential capability. The same goes for smart contracts. In Solidity smart contracts, there are two upgrade methods: Transparent and UUPS. With these two functions, contract proxies and upgrades have become standard in the industry.
How do project teams upgrade contracts? Typically, the contract that users interact with is not the core contract that directly runs the business logic, but a "proxy contract." After receiving user requests, the proxy contract forwards them to the core business contract, which then processes them. Contract upgrades involve changing this; simply put, while smart contracts cannot be modified, the contract that users ultimately access and that runs the business logic can be replaced. This is also a common practice in the industry.
Even the safest contracts, once they undergo a "contract upgrade," have changed their business contracts, rendering previous audit reports obsolete.
In simple terms, the contract you interact with today may be safe, but when you access the same project tomorrow, its security may have fundamentally changed. The contract (or the hacker attacking the contract) may still have the ability to transfer all your authorized assets.
How Dangerous is Unlimited Authorization?
Fortunately, authorization does not mean that users are always exposed to the risk of having their wallets emptied. There is another important rule in the authorization mechanism: authorization is limited in quantity. When users "Approve" a certain amount of tokens, the contract can only utilize that amount, even if there are more of that token in the wallet, the contract cannot access them.
However, the danger lies in the fact that most DeFi contracts recklessly request "unlimited authorization" from users, meaning that by default, the amount of tokens users approve is unlimited.
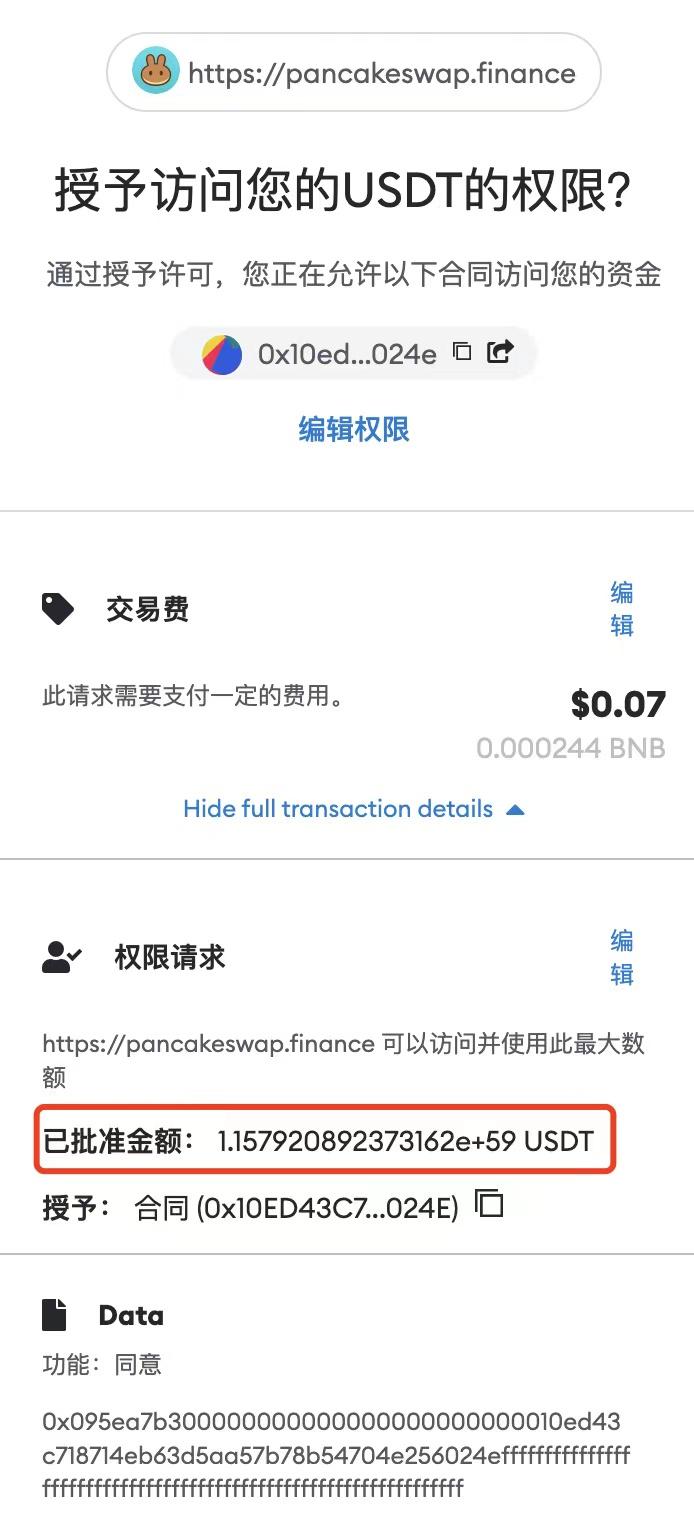
A typical "unlimited authorization" operation, with an authorized amount reaching 10 to the power of 59
How Can Users Protect Themselves?
Without authorization, there is no security risk. When performing on-chain operations, if an "Approve" operation is required, users should follow the principle of "approve as much as you need." If I only need to sell 1000 TOKEN, then I should manually change the Approve amount to 1000. The amount transferred by the contract is cumulative, meaning that if only 1000 is authorized and this transaction happens to be 1000, the contract's authorization limit will be exhausted. Even if the contract poses a security risk in the future, it will no longer be able to transfer any assets from the user's wallet.
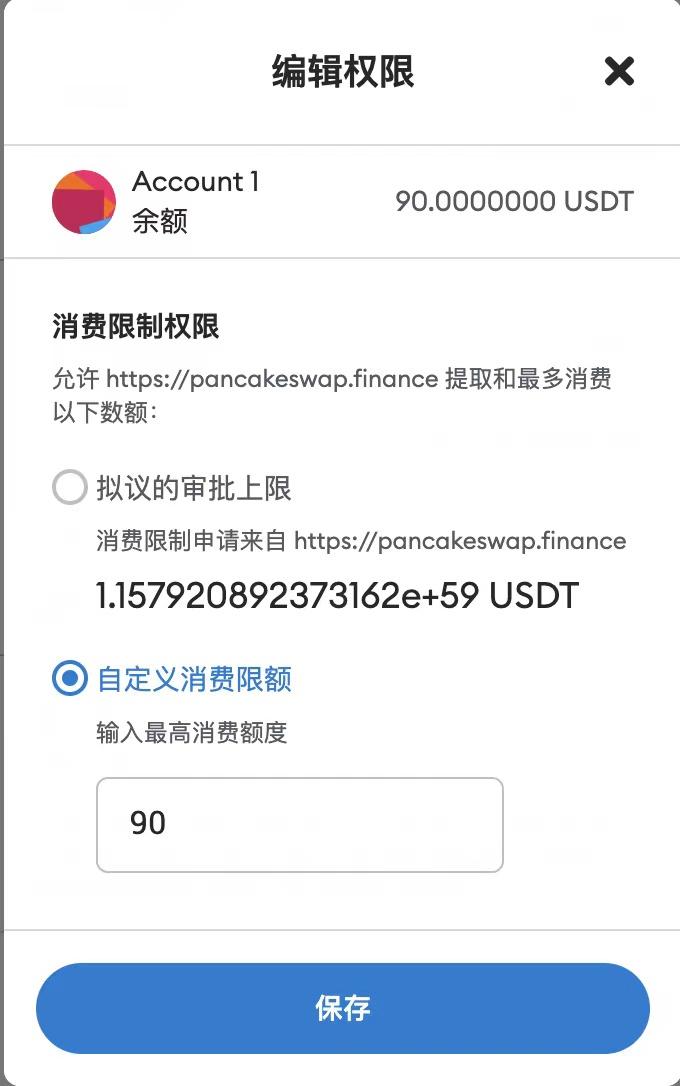
Users can manually modify the authorized amount
For users who have already authorized, they can also initiate a revoke operation. (An interesting detail is that Ethereum does not support "revoking authorization"; this operation essentially grants the contract "0" amount of authorization.)
Commonly used sites for revoking authorization include (recommended by the security company Manwu):
Dappstar: https://tac.dappstar.io/#/
Revoke: https://revoke.cash/
Approved.zone: https://approved.zone/
Rabby Wallet
In addition, some blockchain explorers also support users in viewing and revoking authorizations.
https://cn.etherscan.com/tokenapprovalchecker
https://bscscan.com/tokenapprovalchecker
Who is Responsible for DeFi Theft?
The "dark forest" is a widely circulated narrative about on-chain order, reminding users of the dangers and high risks of this world. But can all such security incidents be entirely attributed to users' lack of security awareness?
In such incidents, the unchecked demand for user authorization by DeFi projects is the initial source of hidden dangers. Almost all projects default to unlimited authorization when requesting authorization. Although users can manually modify it, a responsible market should take on the responsibility of investor protection and user education.
To this day, how many crypto users are still unaware of the dangers of authorization? And in this environment, project teams continue to demand dangerously high unlimited authorization.
The abuse of authorization in DeFi has long become a common practice in the industry, and this high-risk situation almost jeopardizes all users' assets. The far-reaching and extensive impact of this risk is likely unmatched by any other security hazard. This risk fundamentally contradicts the simple intuition that "no one can take the coins in your wallet." This is also a risk and challenge that the industry must continually face.
After the theft incident, Shenyu has called on Twitter, "I urge project teams to regulate the use of authorization functions, approve only as much as needed, and avoid unlimited authorization, so everyone can feel secure."
Decentralization is full of opportunities and risks. Do you remember the original vision of crypto technology? "Protect your assets; no one can take the cryptocurrency in your wallet." Establishing a healthy order requires not complex code or obscure concepts, but ensuring that every ordinary user can safely use crypto technology still requires the collective effort of every participant in the industry.
Popular articles