Decentralization of social networks has become a trend, understanding the core underlying technology choices and routes
This article is from Chain News, authored by Jay Graber, founder of the social platform Happening, and compiled by Zhan Juan.
After more than a year, Twitter founder Jack Dorsey has once again announced major progress on the decentralized social protocol standard bluesky, stating that the team has exchanged ideas with many decentralized community talents since February last year and has publicly released a 61-page overview of the decentralized social ecosystem, introducing the main protocols, applications, and themes currently existing in the ecosystem.
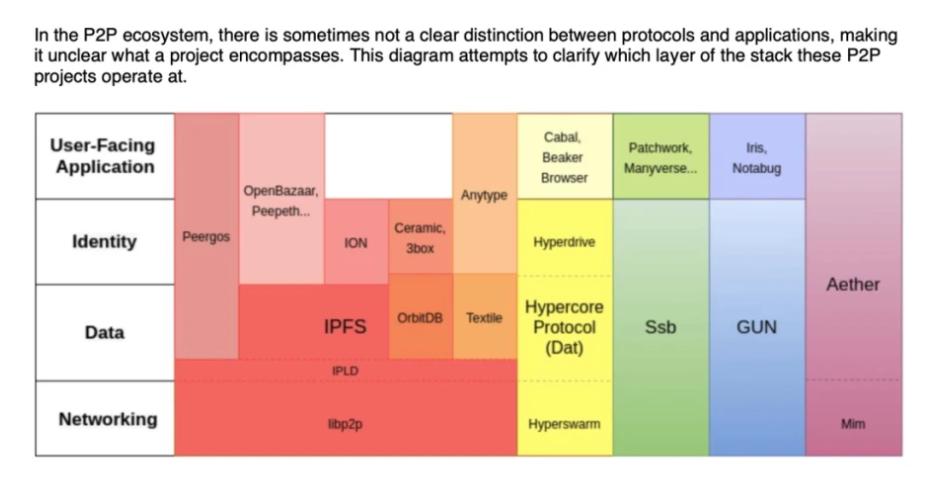
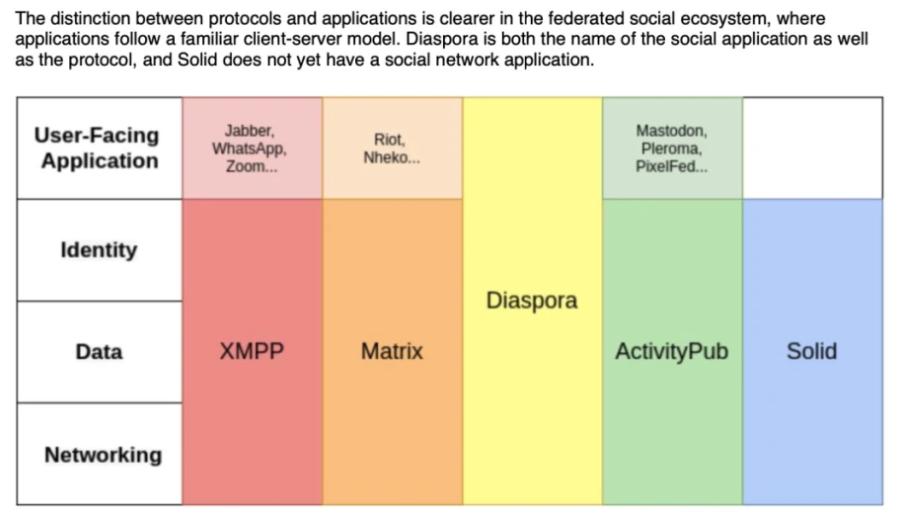
In the overview, protocols like IPFS and Solid are not unfamiliar to internet and blockchain practitioners, but protocols such as ActivityPub, Matrix, Ssb, and Aether are relatively niche; however, they are key protocols in the decentralized social field, structurally divided into federated protocols and peer-to-peer protocols.
In this article, social platform Happening founder Jay Graber clearly introduces the characteristics, representative protocols, and advantages and disadvantages of these two types of protocols to help readers unfamiliar with the field get started.
The efforts to decentralize social networks aim to change the balance of power from a structural perspective, allowing users to easily switch services and control their own identity and data. Describing a network as " decentralized " is merely defining it by what it is not—specifically, it does not rely on a single server cluster operated by a company. As for what it actually is, it can take many different forms.
Federated protocols and peer-to-peer (P2P) protocols are different approaches to designing networks, which can empower users structurally.
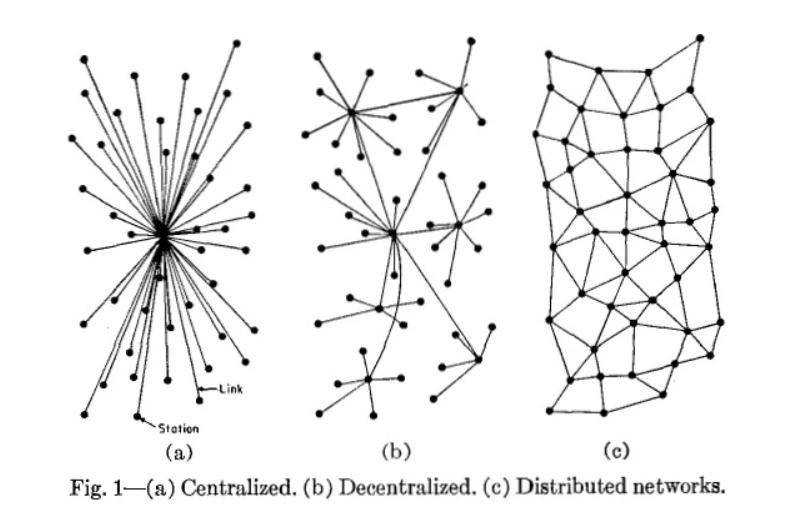
Also referred to as centralized, federated, and peer-to-peer
Traditional social applications, such as Twitter, Facebook, and Instagram, operate on a client-server model. As a user, all your interactions go through a company's server. In a federated network, users still interact with servers, but anyone can run a server and interact with other servers in the network, providing users with more vendor choices. In a P2P network, there is no distinction between client and server. Each user's device can simultaneously act as both, making them functionally equivalent to peers.
This article will outline some of the most popular federated and peer-to-peer social network designs. I will delve into ActivityPub and Ssb, and introduce how their main implementations address challenges such as identity, moderation, and monetization. After a brief comparison of Matrix and Aether, I will describe how some alternative methods operate.
At the end of each section, I will list the main advantages and disadvantages of the federated model and the P2P model.
Blockchain-based social networks will be discussed in subsequent articles.
Federated Protocols
Federated networks allow users to choose a server to register, enabling access to the entire network distributed across many different servers. This provides users with more choices in terms of applications, policies, and community culture. One federated protocol that everyone uses on the internet is email. Gmail is a popular email application, but even if you use another provider, you can still communicate with anyone who has an email address.
ActivityPub
ActivityPub is a federated protocol that defines a set of interoperable social network interactions through specific APIs. Any server implementing this protocol can communicate with other servers in the network.
Mastodon, built on ActivityPub, is a popular federated alternative to Twitter, with about 2.2 million users.
Before Mastodon, projects like GNU social and Diaspora attempted to scale federated social networks but failed. Mastodon's success is largely due to its user interface, which looks and feels very much like Twitter, making it very familiar and allowing dissatisfied users to easily settle in.
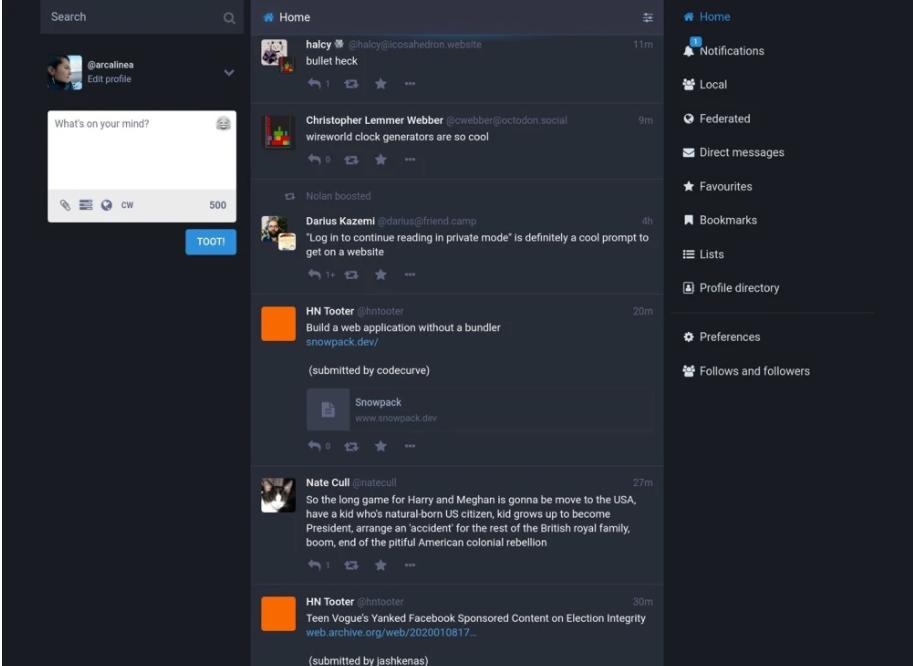
Home feed on Mastodon
Identity
Users create accounts on servers ("instances") but can communicate with users on other instances. The entire group of interoperable instances is referred to as Fediverse. A complete username consists of a user's handle plus the name of the instance they belong to, for example: @arcalinea@mastodon.social.
Account credentials are managed by the user's instance, so if a user forgets their password, they can request a password reset.
Moderation
Each instance sets its own moderation policies, which can be determined unilaterally by administrators or through some form of collective voting. Administrators can ban entire instances, cutting off their visibility. If an instance is disabled by many other instances, its users can still communicate with each other, but they will be isolated from other Fediverse users. This situation occurred with Gab.com, which established an instance.
Monetization
Federated social networks require costs for both hosting and development. Each instance is funded by its own administrators and community. Mastodon's development is funded through Patreon, operated by the main developer. Currently, this application platform generates $70,000 annually, which supports his full-time work on Mastodon and covers the hosting costs for the mastodon.social instance and a moderation team.
Another Federated Protocol: Matrix
Matrix is a protocol designed for chat rather than social networking, but it is worth mentioning for its well-executed federated chat experience and valuable work in improving identity and moderation.
The protocol currently has about 11 million users using various clients. It was developed by New Vector, which raised $8 million in Series A funding in 2019.
Compared to most decentralized protocols, Matrix's identity solution is more flexible—users have a Matrix user ID but can also use third-party IDs. Matrix accounts can be linked to various IDs, such as email addresses, social accounts, and phone numbers. A global federated trusted identity server cluster is used to verify and replicate these mappings. The Matrix team is also actively developing management tools, which are detailed here, and plans to release a P2P implementation soon.
Advantages and Disadvantages of Federated Protocols
Federated networks provide a familiar user experience because users do not have to take full responsibility for their account credentials and can interact with content in ways they are accustomed to. Users can choose different services within the same network to better meet their needs without having to adapt to entirely different ways of doing things.
However, federated servers also inherit some of the same drawbacks as centralized servers. Servers rely on administrators, who are often individuals or organizations with fewer resources than large social media companies. Server administrators may abuse their power or shut down services due to cost issues. For centralized servers, someone can request to block access or provide backdoors, and the same can be done for federated servers.
Depending on the implementation, user identities may be tied to servers, meaning users will lose connections and data when migrating. Privacy protections vary—Mastodon currently does not encrypt content, so all messages, including private messages, may be visible to server administrators.
P2P Protocols
P2P protocols allow users to communicate directly with each other, as all devices in the network are peers, capable of both requesting and responding to data. Some nodes may have special roles, such as public bootstrap nodes that help new users connect to the network, but each node remains functionally equivalent. This design gives users maximum control while also placing the greatest responsibility on them.
Ssb, or secure-scuttlebutt, is a distributed gossip protocol designed for social sharing. Each node has a partial view of the network, making it difficult to count the total number of users, but according to a developer's web crawler run in November 2019, there are about 16,000 nodes on Ssb. Users are distributed across several different client applications, running on desktop (Patchwork) and mobile (Manyverse, Planetary).
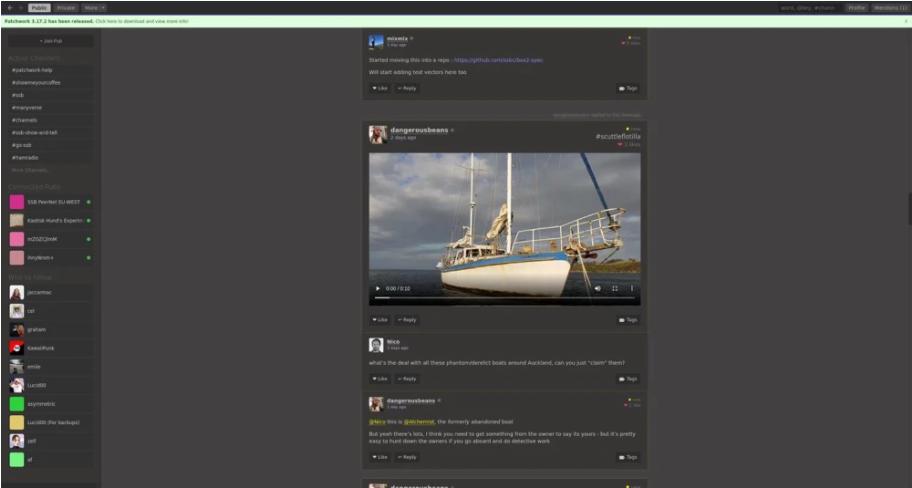
Patchwork, a desktop client for Ssb
Each user has a public/private key pair used to sign posts and verify their authenticity. Each post is attached to the last one, ordered in a log that only appends. Because each post is linked to the last one, it is currently impossible to delete or edit posts. When you follow a user, you will start storing and synchronizing their posts. When you use an Ssb application, it continuously shares data with other nodes in the background.
Identity
In Ssb, users are identified by their public keys. My public key is:
@3QHXrXl762sf7P/Q1RMtscA7IRipfUFnE5tpie5McvE=.ed25519
Users can choose a human-readable nickname associated with their key, but the nickname is not unique, as there is no global registry. Others can mention me with my nickname @arcalinea, but others can also use the same name.
Key management is one of the biggest challenges, as users inevitably lose and forget their passwords. Users have complete control over their identity. This means that if they lose their password, they will permanently lose access to their account. Keys are currently stored on devices, so there is no way to log into an account across multiple devices—this is a fundamental feature in the minds of social network users.
To address the key management issue, the Dark Crystal project within the Ssb ecosystem has implemented a social key recovery system. It splits the key into shards stored with trusted family and friends, who can help reconstruct the lost key.
Moderation
At the Ssb protocol layer, there is a flag feature used to send strong negative signals about bad actors. There is no global moderation or dedicated moderators. Applications built on Ssb allow users to block and ignore. Blocking in Ssb is more powerful than in centralized networks, as it means that the data of blocked users no longer passes through those nodes. If enough people block a user or group of users, that part of the network will become isolated from other parts.
Monetization
P2P network maintainers do not incur hosting costs because there are no servers, and the network capacity naturally grows as new users join. Developers who want to do more volunteer work need to find funding themselves. The Ssb ecosystem is supported through various grants, donations, income from part-time projects and consulting, and some companies that have raised funds to build applications on Ssb.
Another P2P Protocol: Aether
Aether is a P2P social network similar to Reddit. Its data structure is a DAG (Directed Acyclic Graph) rather than a purely append-only log; it also limits the appearance time of posts, allowing you to edit and delete posts, and posts will be automatically deleted after a period of inactivity, unlike Ssb, which stores every post.
The P2P version is supported by funding from the Aether Pro version. It allows multi-device login—you can store and synchronize encrypted keys from a remote backend. Each sub-community has its own moderators, who can be elected by the community or impeach themselves.
Advantages and Disadvantages of P2P
P2P networks allow users to fully control their data and identity. The data layer is functionally separated from the application view, so users can seamlessly switch between applications while retaining all accumulated posts and connections. The capacity of P2P networks naturally expands with demand, as new users add resources to the network rather than just consuming.
P2P networks have maximum resilience and anti-censorship capabilities. Since P2P networks do not require servers, as long as there is a local connection between two devices on the network, applications can continue to work even if other parts of the internet are down. Accounts have encrypted key pairs, so private messages are easily supported—Ssb provides end-to-end encrypted private messages.
However, the flip side of control is taking responsibility. There is no service to help recover lost or stolen passwords. Moderation relies on bottom-up methods that have not been tested on a large scale, which means these networks can experience similar abuses as centralized sites. Storing data in the background or running gossip protocols on P2P can consume disproportionate resources on user devices. P2P networks do not have global "like" or "share" counts, and some do not allow users to edit or delete posts.
This practice may be surprising, but it illustrates that replicating the familiar features and performance of users in P2P networks is indeed challenging. A larger technical challenge is that networks are built around the assumptions of the client-server model, so a network trying to be fully P2P must delve into very low layers and deal with issues like NAT traversal.
Some disadvantages of federated protocols and P2P protocols may be overcome in the future. Research and development in key areas such as key management, identity, and moderation will help significantly improve usability. One barrier is that current implementations still lack resources—all the projects listed above have raised some funding through donations, grants, or venture capital, but none have developed a sustainable business model.
Another barrier is that the development of decentralized protocols is inherently slower than centralized applications, as updating protocols and getting all clients involved requires community coordination. Standard organizations like W3C often emerge to coordinate updates; otherwise, over time, incompatibilities between different implementations could lead to network fragmentation.
As it stands, centralized applications are easier to build, iterate faster, and are easier to monetize, but a passionate community has been dedicated to decentralized alternatives, as these technological architectures can change the relationship between users and platforms, providing users with more choices.
Popular articles